Perkoon vs Phishly
Side-by-side comparison to help you choose the right product.
Send files directly to anyone for free with unlimited peer-to-peer transfers.
Last updated: March 4, 2026
Phishly
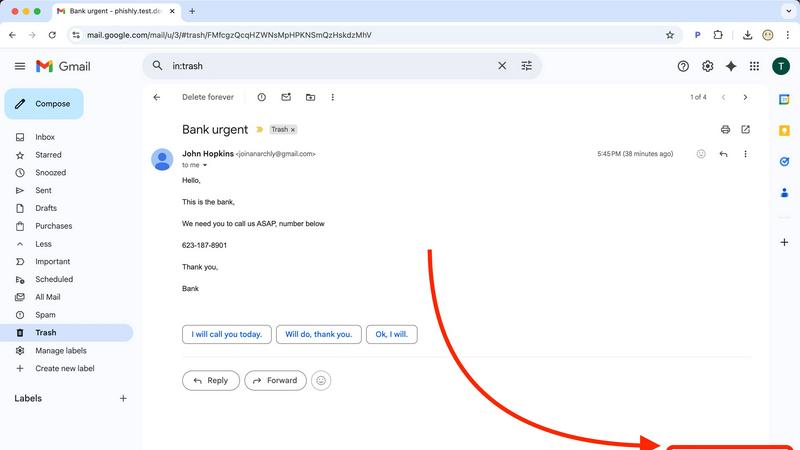
Phishly uses AI to instantly detect phishing emails in your Gmail inbox.
Visual Comparison
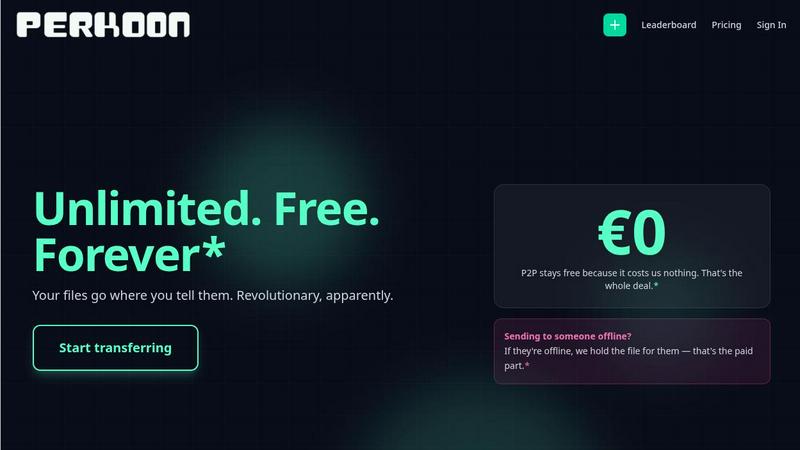
Perkoon
Phishly
Feature Comparison
Perkoon
Truly Free Peer-to-Peer (P2P) Transfers
Perkoon's core feature is its unlimited, free P2P file transfer. When both sender and recipient are online, files are beamed directly from one browser to another without ever passing through Perkoon's servers. This means there are no file size limits, no mandatory sign-ups, and absolute privacy for your data. Because this method costs Perkoon virtually nothing to facilitate, they can offer it as a free service forever, with no hidden catches or data monetization.
Honest Encrypted Cloud Storage
For sending files to someone who is offline, Perkoon provides encrypted cloud storage as a paid feature. This approach is transparent: the free P2P model covers online transfers, while the paid cloud storage honestly covers the cost of running and maintaining secure servers. Your files are encrypted on their servers, providing a secure holding area until your recipient is ready to download, without pretense of it being free.
Native AI and Automation Integration
Perkoon is designed for the modern workflow by offering built-in tools for automation and AI agents. Through features like window.__perkoon, AI assistants and scripts can interact with the service programmatically without resorting to inefficient screen-scraping techniques. This makes it possible to integrate file sending and receiving into automated pipelines, agentic workflows, and custom tools seamlessly.
Simple CLI and Browser Tools
Beyond the web interface, Perkoon offers a Command Line Interface (CLI) tool, providing power users and developers with a fast, scriptable way to transfer files. The web service itself works optimally on modern browsers like Chrome, Edge, and Brave, with clear communication about any limitations on Firefox and Safari, ensuring a reliable experience across platforms.
Phishly
One-Click Gmail Integration
Phishly operates seamlessly within your existing workflow as a lightweight Chrome extension. Once installed, a "Scan with Phishly" button appears directly in your Gmail interface. When you open any email that raises suspicion, a single click initiates a comprehensive AI analysis without you having to copy, paste, or navigate away from your inbox. This frictionless integration ensures that security checks are effortless, encouraging regular use and making safe email habits easy to maintain.
AI-Powered Multi-Indicator Detection
The core intelligence of Phishly lies in its trained AI model, which scrutinizes emails across multiple threat vectors simultaneously. It doesn't rely on a single check but evaluates a combination of factors including suspicious domain names and URLs, grammatical inconsistencies, the use of urgent or threatening language designed to provoke a quick response, attempts to spoof legitimate sender addresses, and sophisticated social engineering tactics. This holistic approach catches a wider range of phishing attempts, from crude scams to highly targeted spear-phishing campaigns.
Clear, Actionable Risk Assessment
After analysis, Phishly doesn't just provide a raw score or complex technical data. It delivers a straightforward, color-coded verdict: Safe, Medium Risk, or High Risk. Each result is accompanied by a detailed breakdown explaining exactly which red flags were detected. For example, it might highlight that the sender's domain is misspelled, the link points to an unsecured website, and the language creates an artificial sense of urgency. This transparency helps you understand the threat and learn to identify similar patterns in the future.
Privacy-First Web Tool for Any Email
For emails received outside of Gmail or for those who prefer not to use an extension, Phishly offers a versatile web-based tool. You can simply copy the full headers and content of any suspicious email—from Outlook, Apple Mail, or any other client—and paste it into the tool on the Phishly website for an instant, private analysis. This method guarantees that Phishly never automatically accesses your inbox; it only ever analyzes the specific text you provide, putting you in complete control of your data.
Use Cases
Perkoon
Sending Large Project Files to Clients
Freelancers and agencies can use Perkoon's free P2P transfer to send large video edits, design mockups, or code repositories to clients instantly. There's no need to compress files or upgrade to a "pro" plan just to bypass a size limit. If the client is unavailable, the secure cloud hold ensures the file waits for them.
Private Document Exchange
For lawyers, journalists, or anyone handling sensitive information, Perkoon's P2P mode is ideal. Since files travel directly between browsers and are never stored on an intermediary server, it provides a much higher degree of privacy and security for confidential documents compared to traditional cloud transfer services.
Automating Backup and Sync Tasks
Developers and IT professionals can leverage Perkoon's CLI and native automation APIs to build custom scripts. For example, you can automatically back up log files to a colleague's machine or sync generated reports directly from a server process to a team storage bucket, all without manual intervention.
AI Agent File Operations
When an AI agent needs to send a generated image, document, or dataset to a user, it can use Perkoon's built-in window.__perkoon interface directly. This allows AI assistants to perform file transfer tasks reliably as part of a larger automated workflow, instead of struggling with simulated clicks on a website designed for humans.
Phishly
Verifying Urgent Financial or Work Requests
You receive an email from your CEO or a colleague urgently requesting a wire transfer, gift card purchase, or sensitive company data. The request feels unusual, but the pressure to comply is high. Instead of acting immediately or spending time manually investigating, you click "Scan with Phishly." The AI can detect if the sender's email is subtly spoofed or if the language uses classic social engineering pressure tactics, giving you the evidence needed to pause and verify the request through another channel, potentially preventing a devastating business email compromise (BEC) attack.
Checking Legitimacy of Account Security Alerts
A concerning email arrives claiming to be from your bank, PayPal, or Netflix, stating your account is compromised and urging you to click a link to "secure it." These are among the most common and effective phishing lures. With Phishly, you can instantly scan the email. The AI will analyze the link destination (often a fake login page), check for inconsistencies in the sender's address, and assess the alarming tone, providing a clear risk level so you can safely ignore the scam and contact the service directly through their official website or app.
Screening Marketing Offers and Prize Notifications
Too-good-to-be-true offers, lottery wins you didn't enter, or exclusive deal notifications can be phishing attempts to harvest personal information or distribute malware. When curiosity strikes, use Phishly to scan these emails. The tool will evaluate the credibility of the sending domain, look for hidden tracking pixels or malicious attachments, and analyze the content for deceptive promises, helping you distinguish between a legitimate promotional email and a fraudulent trap designed to exploit your interest.
Educating Teams and Family on Phishing Signs
For small business owners or individuals concerned about less tech-savvy family members, Phishly serves as an excellent educational tool. By scanning suspicious emails together and reviewing the detailed breakdown of detected risks—like a mismatched "reply-to" address or a disguised hyperlink—you can provide concrete, real-world examples of what phishing looks like. This hands-on demonstration is far more effective than abstract advice, building critical thinking and safer email habits for everyone involved.
Overview
About Perkoon
Perkoon is a file transfer service designed to solve the core problem of moving files from one point to another without the typical friction, privacy invasions, and hidden costs. It is built for individuals, freelancers, and teams who are tired of artificial file size limits, mandatory account creation, and services that monetize user data. Perkoon's main value proposition is its refreshingly honest and technically elegant two-mode system. Its flagship offering is a completely free, unlimited peer-to-peer (P2P) transfer service that works directly between browsers when both parties are online, ensuring privacy and eliminating operational costs. For situations where the recipient is offline, Perkoon offers a straightforward paid cloud storage option, transparently priced to cover server costs. Uniquely, Perkoon is natively built for automation, featuring tools that allow AI agents and scripts to interact with the service directly, making it a future-proof solution for both people and the machines that assist them.
About Phishly
Phishing attacks are a constant, evolving threat designed to trick you into revealing sensitive information. Phishly is the practical, AI-powered solution that puts powerful detection in your hands, instantly. It's a simple Chrome extension for Gmail and a web-based tool that acts as your personal security analyst. When you receive an email that seems off—whether it's an urgent request from your "boss," a too-good-to-be-true offer, or a suspicious link from a familiar service—you can scan it with one click. Phishly's advanced AI instantly analyzes the content for classic phishing indicators like spoofed sender addresses, deceptive domains, manipulative language, and hidden threats. It then provides a clear, actionable risk assessment: Safe, Medium Risk, or High Risk, complete with a plain-English explanation of what it found. Designed for individuals, remote workers, and small to medium businesses, Phishly offers enterprise-grade detection without the complexity or cost. It respects your privacy by only scanning emails you explicitly choose to analyze, requires no technical setup, and is completely free to use. In a world of sophisticated scams, Phishly delivers the instant clarity and confidence you need to navigate your inbox safely.
Frequently Asked Questions
Perkoon FAQ
Do you store my files?
For P2P transfers, your files never touch our servers; they go directly from the sender's browser to the recipient's. For cloud transfers (used when the recipient is offline), files are encrypted and stored temporarily on our servers to facilitate the delivery. We are transparent that this is the part of the service that incurs a cost.
Can Perkoon see what I'm sending in a P2P transfer?
No. In a P2P transfer, the data stream is established directly between the two browsers involved. Our servers only help set up the connection but cannot intercept or see the actual file data being transferred. We literally cannot see what you are sending.
Why is the P2P transfer free forever?
The P2P technology we use allows browsers to connect directly to each other. This process costs us very little in terms of server resources and bandwidth. Therefore, we can offer it for free indefinitely. We only charge for the cloud storage feature, which genuinely requires us to maintain and pay for server infrastructure.
What if the other person is offline?
If your recipient is not online to receive the direct P2P transfer, Perkoon offers an encrypted cloud storage option. You can upload the file to our secure servers, and we will hold it for your recipient to download at their convenience. This is a paid feature, and details can be found on our pricing page.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built with a strict privacy-first principle. The Chrome extension only activates when you explicitly click the "Scan with Phishly" button on an open email. It does not automatically scan, read, or store any emails from your inbox. The web tool only analyzes the specific text you copy and paste into it. We do not store personal data or email content after the analysis is complete. You are always in control of what gets scanned.
Is Phishly really free to use?
Yes, Phishly is completely free to use. Our goal is to make essential phishing protection accessible to everyone, from individuals to small businesses. You can use the Chrome extension for Gmail and the web-based analysis tool without any cost, subscription, or tiered limits. We believe effective cybersecurity should not be a financial barrier.
What makes Phishly different from my email provider's spam filter?
Your email provider's spam filter works automatically in the background to catch obvious spam, but sophisticated phishing emails are designed to bypass these filters by mimicking legitimate correspondence. Phishly acts as your second layer of defense for the emails that land in your primary inbox. It allows you to proactively investigate and analyze any email that triggers your suspicion, providing a detailed, human-readable explanation of potential threats that a generic spam filter does not offer.
Do I need technical knowledge to use Phishly?
Absolutely not. Phishly is designed for ease of use by anyone. Installing the Chrome extension is as simple as adding it from the Chrome Web Store. From there, using it requires just one click in Gmail. The results are presented in plain language with clear risk categories (Safe, Medium, High) and straightforward explanations, requiring no technical expertise to understand and act upon.