iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
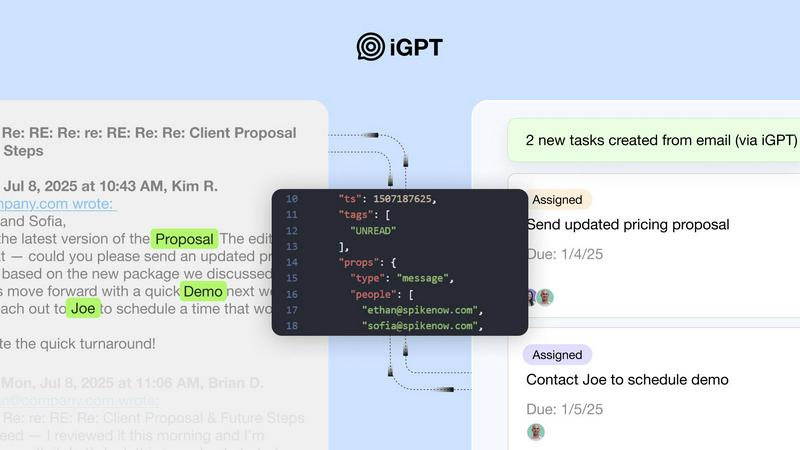
iGPT gives AI agents secure, contextual answers directly from your team's email and attachments.
Last updated: February 28, 2026
Threat Watch
Quickly assess your cybersecurity health and gain vital insights to safeguard against threats and breaches.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch

Feature Comparison
iGPT
Unified Intelligence Endpoint
Replace complex, multi-step retrieval architectures with a single API call. iGPT consolidates the entire process—from understanding your natural language query to retrieving relevant data across emails and attachments, shaping the optimal context, and delivering a reasoned response—into one streamlined pipeline. This eliminates the need to manage separate systems for parsing, vector stores, and prompt chains, dramatically accelerating development.
Deep Email & Attachment Processing
iGPT goes beyond simple email text. It automatically and deeply indexes the full content of email conversations, including reconstructing threads across time and participants. Crucially, it processes attachments—extracting text, data, and structure from documents, PDFs, and spreadsheets—to understand the complete context of a communication, ensuring no critical information buried in a file is missed.
Context Engineering Framework (CEF)
This proprietary system automatically optimizes how context is retrieved and presented to your LLM. It employs hybrid retrieval (semantic, keyword, and filters), scores and re-ranks results, and shapes the context window specifically for your query. This means developers get high-quality, relevant context without the manual, iterative work of prompt engineering and tuning, leading to more accurate and reliable agent outputs.
Enterprise-Grade Security & Governance
iGPT is built with strict compliance and data control in mind. It features a zero-data training policy, ensuring your data is never used to improve models. It offers Role-Based Access Control (RBAC) with OAuth enforcement, processes data in memory with zero retention, and provides a full audit trail for every request. This allows enterprises to leverage powerful AI while keeping data securely within their control.
Threat Watch
Comprehensive Security Assessments
Threat Watch provides thorough evaluations across critical security categories, assessing your organization’s assets, vulnerabilities, and potential exposures to give you a complete picture of your cybersecurity health.
Real-Time Insights
With its real-time monitoring capabilities, Threat Watch delivers immediate alerts and insights into potential threats, ensuring that your organization can act promptly to mitigate risks and safeguard its assets.
Automated Risk Prioritization
The platform utilizes advanced algorithms to prioritize risks based on their potential impact, allowing security teams to focus their efforts on the most critical vulnerabilities that could affect their organization.
User-Friendly Reporting
Threat Watch offers robust reporting features that present complex data in an easily digestible format, helping stakeholders understand cybersecurity metrics and make informed decisions to enhance security measures.
Use Cases
iGPT
AI-Powered Email Assistants
Build intelligent agents that can draft, prioritize, summarize, and act on email with full historical and attachment context. Instead of agents working in a vacuum, they can understand the entire conversation thread, participant sentiments, and referenced documents to generate highly relevant and actionable responses, turning your inbox into an automated productivity hub.
Customer Support & Success Copilots
Empower support teams with agents that instantly rebuild the complete customer story. By analyzing long email chains, attachments, and subtle tone shifts, iGPT provides copilots with a unified view of the issue history, past resolutions, and outstanding commitments. This leads to faster, more personalized support and higher customer satisfaction.
Sales & CRM Intelligence Automation
Automatically extract crucial deal intelligence directly from email threads. iGPT can identify key decisions, action items, owners, deadlines, and changes in deal momentum that are often communicated informally over email. This data can be pushed to CRM systems, giving revenue teams real-time, context-rich insights without manual entry.
Compliance & Audit Trail Generation
Automate the tracking of approvals, feedback, and rationale buried in email communications. iGPT can trace specific decisions or statements back to their source messages and attachments, creating a verifiable audit trail. This is essential for legal, financial, and regulatory compliance, saving countless hours of manual email discovery.
Threat Watch
Small Business Cybersecurity
Small businesses can leverage Threat Watch to identify vulnerabilities in their systems and receive actionable insights tailored to their specific needs, helping them protect their sensitive data against cyber threats.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to conduct comprehensive assessments across multiple departments, ensuring that every aspect of their cybersecurity posture is monitored and fortified against potential attacks.
Incident Response Preparation
Organizations can use Threat Watch to prepare for potential cybersecurity incidents by identifying weaknesses in their defenses and developing response strategies to minimize damage should an attack occur.
Compliance and Regulation Adherence
Threat Watch aids companies in complying with industry regulations by providing the necessary assessments and reports that demonstrate their commitment to maintaining a secure and resilient cybersecurity environment.
Overview
About iGPT
iGPT is an enterprise-grade email intelligence API designed to solve a critical and costly problem: the failure of standard AI to understand the complex, unstructured data within business email communications. Email is where real work happens, containing vital context across threads, attachments, and participant dynamics, yet this richness is often lost on AI agents. iGPT acts as a secure and auditable gateway, enabling AI agents and automated workflows to access, comprehend, and leverage this buried context. Built for developers and enterprises, it serves teams building agentic systems, sales intelligence platforms, customer success tools, and compliance solutions that require deep, real-time insight from communication data. Its core value proposition is delivering trusted, context-aware answers from messy email data through a single, unified API call. This eliminates the traditional engineering heavy-lifting of parsing, chunking, indexing, and endless prompt tuning. Instead, iGPT offers a streamlined pipeline that handles intelligent retrieval, context shaping, and reasoning automatically. With a foundational focus on end-to-end security, granular access controls, and comprehensive audit trails, iGPT empowers businesses to deploy powerful, context-aware AI agents with confidence while maintaining strict data governance and compliance standards.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to help organizations protect their digital assets effectively. It offers a comprehensive analysis of critical security categories, allowing businesses to evaluate their assets, vulnerabilities, and exposures in detail. Threat Watch is designed for organizations of all sizes, from startups to large enterprises, that prioritize strengthening their cybersecurity framework. The platform's main value proposition lies in its ability to deliver real-time insights and automated assessments, enabling teams to identify, prioritize, and proactively mitigate risks. With its user-friendly interface and advanced reporting capabilities, Threat Watch simplifies the often complex landscape of cybersecurity, helping organizations respond to threats swiftly and maintain a robust digital environment. Additionally, it uncovers your organization’s cybersecurity health quickly, ensuring that you can act decisively in the face of evolving threats.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is architected for enterprise security. It operates on a zero-data training and zero-data retention policy, meaning your data is never used to train models and is not stored after processing. All inferences happen in memory. It enforces strict OAuth-based Role-Based Access Control (RBAC) and provides full audit trails, ensuring data never leaves your company's control and every access is traceable.
What types of email sources and attachments can it connect to?
iGPT can connect to enterprise email systems like Google Workspace and Microsoft 365 via secure OAuth. It deeply indexes email content and threads. For attachments, it processes a wide range of formats, including PDFs, Word documents, Excel spreadsheets, and PowerPoint presentations, extracting text and structural data to understand the full context of the communication.
Do I need to manage vector databases or complex prompt chains?
No. A core benefit of iGPT is that it abstracts away this infrastructure complexity. You do not need to set up parsing, chunking, vector stores, or design intricate prompt chains. The unified API and its built-in Context Engineering Framework handle retrieval, context optimization, and reasoning automatically based on your simple natural language query.
What is the Context Engineering Framework (CEF)?
The Context Engineering Framework (CEF) is iGPT's intelligent retrieval and reasoning pipeline. It automatically performs hybrid search (combining semantic and keyword techniques), filters, re-ranks results, and optimally shapes the context window for your specific query and chosen LLM. It delivers high-quality context so you don't have to manually tune prompts, ensuring faster and more reliable outcomes.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is suitable for organizations of all sizes, from small startups to large enterprises, that are looking to enhance their cybersecurity measures and protect their digital assets.
How does Threat Watch provide real-time insights?
Threat Watch continuously monitors your organization’s systems and networks, automatically identifying and alerting you to potential threats as they arise, enabling swift action to mitigate risks.
Can Threat Watch help with compliance requirements?
Yes, Threat Watch is designed to assist organizations in meeting compliance requirements by providing comprehensive assessments and detailed reporting that align with industry regulations.
Is the platform easy to use for non-technical staff?
Absolutely. Threat Watch features a user-friendly interface that simplifies the complexities of cybersecurity, making it accessible for users with varying levels of technical expertise.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade email intelligence API that falls into the business intelligence category. It specializes in giving AI agents secure, contextual answers from complex email threads and attachments, eliminating the heavy engineering typically required to process unstructured communication data. Users often explore alternatives for various practical reasons. These can include budget constraints, the need for different feature sets like integration with other data sources, or specific platform requirements that may not align with a single vendor's offering. It's a natural part of the evaluation process for any technical solution. When assessing other options, focus on core capabilities. Key considerations should be the depth of email and attachment understanding, the robustness of security and audit controls, the simplicity of the developer API, and the system's ability to reconstruct full conversation narratives in real time. The right tool should reliably turn messy email data into actionable intelligence without creating new operational burdens.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cyber health and protect their digital assets. It fits into the business intelligence category, offering real-time insights, automated risk assessments, and dark web monitoring among its key features. Users often seek alternatives to Threat Watch for various reasons, including budget constraints, specific feature requirements, or compatibility with existing platforms. When searching for an alternative, it’s crucial to consider factors such as the comprehensiveness of security assessments, the ease of use of the interface, the relevance of features to your organization's needs, and the level of support provided. Prioritizing these criteria will ensure that you choose a solution that effectively enhances your cybersecurity posture.