Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right product.
Opal44 delivers AI-driven insights from your website traffic in plain English, making analytics simple and actionable.
Last updated: March 4, 2026
Threat Watch
Quickly assess your cybersecurity health and gain vital insights to safeguard against threats and breaches.
Last updated: March 1, 2026
Visual Comparison
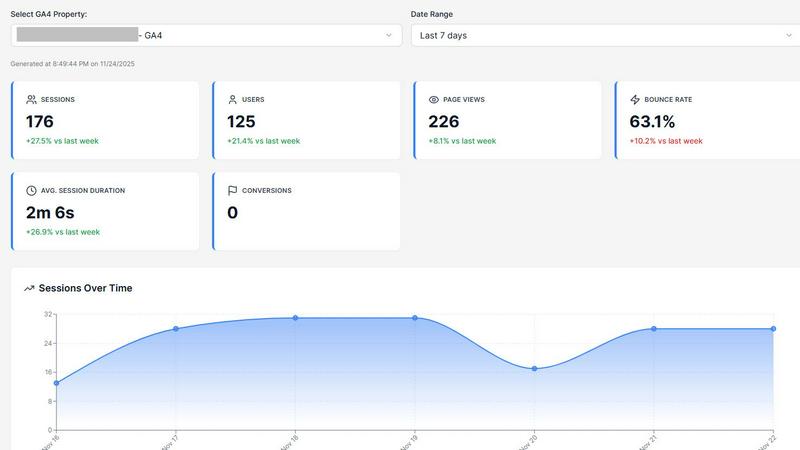
Opal44
Threat Watch

Feature Comparison
Opal44
Plain English Insights
Opal44's AI connects directly to your GA4 data, interpreting metrics and trends in simple, everyday language. This feature eliminates the need for technical expertise, making it easy for anyone to understand what's happening with their website traffic.
Conversation-Style Reports
Reports generated by Opal44 resemble a friendly conversation, guiding users through their analytics as if they were chatting with a personal analytics advisor. This engaging format ensures that insights are not only clear but also enjoyable to read.
Smart, Data-Driven Tips
The platform provides tailored recommendations based on your GA4 data, helping users improve website traffic and overall performance. These actionable tips are designed to empower users to make data-driven decisions that yield results.
Real-Time Alerts
With Opal44, users receive instant notifications when significant changes occur in their traffic data, such as sudden spikes or drops. This feature ensures that you are always aware of your website's performance and can react promptly to any unusual activity.
Threat Watch
Comprehensive Security Assessments
Threat Watch provides thorough evaluations across critical security categories, assessing your organization’s assets, vulnerabilities, and potential exposures to give you a complete picture of your cybersecurity health.
Real-Time Insights
With its real-time monitoring capabilities, Threat Watch delivers immediate alerts and insights into potential threats, ensuring that your organization can act promptly to mitigate risks and safeguard its assets.
Automated Risk Prioritization
The platform utilizes advanced algorithms to prioritize risks based on their potential impact, allowing security teams to focus their efforts on the most critical vulnerabilities that could affect their organization.
User-Friendly Reporting
Threat Watch offers robust reporting features that present complex data in an easily digestible format, helping stakeholders understand cybersecurity metrics and make informed decisions to enhance security measures.
Use Cases
Opal44
Small Business Optimization
For small business owners, Opal44 offers a straightforward way to analyze website performance without needing extensive analytics knowledge. Users can easily identify traffic trends and optimize their marketing strategies accordingly.
E-commerce Growth
E-commerce managers can leverage Opal44's insights to understand customer behavior better. The actionable recommendations help increase conversion rates, ultimately driving sales and revenue growth.
Client Reporting for Agencies
Digital agencies can use Opal44 to present clear and concise analytics reports to their clients. The plain English insights enhance client understanding, making strategy meetings more productive and effective.
Content Marketing Enhancement
Content creators benefit from Opal44 by receiving insights that guide their content strategies. By understanding what resonates with their audience, they can create targeted content that drives engagement and traffic.
Threat Watch
Small Business Cybersecurity
Small businesses can leverage Threat Watch to identify vulnerabilities in their systems and receive actionable insights tailored to their specific needs, helping them protect their sensitive data against cyber threats.
Enterprise Risk Management
Large enterprises can utilize Threat Watch to conduct comprehensive assessments across multiple departments, ensuring that every aspect of their cybersecurity posture is monitored and fortified against potential attacks.
Incident Response Preparation
Organizations can use Threat Watch to prepare for potential cybersecurity incidents by identifying weaknesses in their defenses and developing response strategies to minimize damage should an attack occur.
Compliance and Regulation Adherence
Threat Watch aids companies in complying with industry regulations by providing the necessary assessments and reports that demonstrate their commitment to maintaining a secure and resilient cybersecurity environment.
Overview
About Opal44
Opal44 is an innovative analytics tool designed to simplify the way businesses understand their website traffic through Google Analytics 4 (GA4). It empowers users with AI-powered insights that translate complex data into plain, actionable English, eliminating the confusion often associated with traditional analytics platforms. Opal44 is ideal for small to large organizations, marketing teams, content creators, and anyone looking to gain a clearer understanding of their website performance without the technical jargon. With features like conversation-style reports, real-time alerts, and smart, data-driven recommendations, Opal44 helps users make informed decisions to optimize their online presence and boost results. The primary value proposition lies in its ability to provide meaningful insights quickly and easily, making analytics accessible to everyone.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to help organizations protect their digital assets effectively. It offers a comprehensive analysis of critical security categories, allowing businesses to evaluate their assets, vulnerabilities, and exposures in detail. Threat Watch is designed for organizations of all sizes, from startups to large enterprises, that prioritize strengthening their cybersecurity framework. The platform's main value proposition lies in its ability to deliver real-time insights and automated assessments, enabling teams to identify, prioritize, and proactively mitigate risks. With its user-friendly interface and advanced reporting capabilities, Threat Watch simplifies the often complex landscape of cybersecurity, helping organizations respond to threats swiftly and maintain a robust digital environment. Additionally, it uncovers your organization’s cybersecurity health quickly, ensuring that you can act decisively in the face of evolving threats.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 connect to Google Analytics 4?
Opal44 securely connects to your GA4 account without requiring any coding skills. The setup process is quick, taking only a few minutes to start receiving valuable insights.
Is my data safe with Opal44?
Absolutely. Opal44 prioritizes your data security and privacy. Your GA4 data is never sold or shared with third parties, ensuring that your information remains confidential and under your control.
What kind of support does Opal44 offer?
Opal44 provides robust customer support, including email assistance for all users. Higher-tier plans also include priority support and onboarding to help you maximize the platform's features.
Can I try Opal44 before committing to a subscription?
Yes! New users can enjoy a 7-day free trial with 50 actions, allowing you to explore all features without any credit card requirement. This trial is a great way to see how Opal44 can transform your analytics experience.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is suitable for organizations of all sizes, from small startups to large enterprises, that are looking to enhance their cybersecurity measures and protect their digital assets.
How does Threat Watch provide real-time insights?
Threat Watch continuously monitors your organization’s systems and networks, automatically identifying and alerting you to potential threats as they arise, enabling swift action to mitigate risks.
Can Threat Watch help with compliance requirements?
Yes, Threat Watch is designed to assist organizations in meeting compliance requirements by providing comprehensive assessments and detailed reporting that align with industry regulations.
Is the platform easy to use for non-technical staff?
Absolutely. Threat Watch features a user-friendly interface that simplifies the complexities of cybersecurity, making it accessible for users with varying levels of technical expertise.
Alternatives
Opal44 Alternatives
Opal44 is an innovative tool designed to provide AI-powered insights into website traffic, specifically utilizing data from Google Analytics 4. As a product within the Business Intelligence category, it aims to simplify complex analytics into easy-to-understand, actionable insights. Users frequently seek alternatives to Opal44 due to various reasons such as pricing concerns, feature sets, or specific platform compatibility needs that may not be met by Opal44. When searching for an alternative, it’s essential to consider factors like the ease of use, the ability to generate clear and actionable insights, and whether the platform offers the specific features that align with your business goals. Additionally, evaluating the pricing structure and customer support options can help ensure that the chosen tool meets both budgetary and operational requirements.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cyber health and protect their digital assets. It fits into the business intelligence category, offering real-time insights, automated risk assessments, and dark web monitoring among its key features. Users often seek alternatives to Threat Watch for various reasons, including budget constraints, specific feature requirements, or compatibility with existing platforms. When searching for an alternative, it’s crucial to consider factors such as the comprehensiveness of security assessments, the ease of use of the interface, the relevance of features to your organization's needs, and the level of support provided. Prioritizing these criteria will ensure that you choose a solution that effectively enhances your cybersecurity posture.